This Week in Data Breaches: Equifax Insider Trading, Another Massive Leak, and more.
This past year, we have been rocked by massive data breaches (Equifax, Cambridge Analytica, and more) and the gross neglect from centralized entities entrusted with our private information. Finally, at the global stage, we are now having important conversations surrounding consumer data and the rights individuals should have when it comes to protecting their personal information.
It’s more important than ever for consumers to take back their data and really examine the standards we should uphold when it comes to consumer data privacy.
This week, Equifax employees were charged with insider trading and a new data leak was reported which exposed the most private information and habits of over 340 million individuals.
Equifax Employees Charged with Insider Trading
In the aftermath of last year’s data breach, researchers have done a deep dive to expose the depth of the damage and assess the clean up. New findings have since come out about how executives conducted themselves during the breach. The Equifax breach was notable not only in the tremendous scale of the breach, but also in the gross mismanagement and misconduct from the company. The company reportedly discovered the breach in July, but it wasn’t publicly reported until September. During this time frame, several executives sold shares, based on insider information.
Last week, a former Equifax software development manager was charged with insider trading. Those who suspiciously sold Equifax stock during this time frame includes several executives such as their Chief Financial Officer and a former chief information officer who was investigated earlier this year. A committee composed of independent Equifax board members has since cleared several of them.
Richard Best, director of the SEC’s Atlanta bureau, said in a statement Thursday, “Corporate insiders simply cannot abuse their access to sensitive information and illegally enrich themselves.”
Suspicions of the trades were first raised after Equifax detailed the timing of the breach, which impacted more than 145 million U.S. consumers who are now vulnerable to identity theft as the hackers likely accessed Social Security and driver’s license numbers, birth dates and addresses.
Continued Problems with Protecting Consumer Data: More Leaks
Another Leak Reported This Week
Within the past week, there has been an even more significant reported data leak. A security researcher found that Exactis, a Florida-based data broker had exposed a database that contained close to 340 million individual records on a publicly accessible server. The exposed database included details for each individual listed, including phone numbers, home addresses, email addresses, and information about the person’s habits and children.
The researcher found the exposed database while searching for ElasticSearch databases visible on publicly accessible servers with American IP addresses. Soon, he found the Exactis database, unprotected by any firewall. While it’s not known if the database has been accessed by any malicious parties, the database was vulnerable for unknown period of time.
Wired reports, “Aside from the sheer breadth of the Exactis leak, it may be even more remarkable for its depth: Each record contains entries that go far beyond contact information and public records to include more than 400 variables on a vast range of specific characteristics: whether the person smokes, their religion, whether they have dogs or cats, and interests as varied as scuba diving and plus-size apparel.”
The database did not include financial information or Social Security numbers, which is the most information most useful to hackers for identity theft, but it does expose individuals to social engineering hacks. It is possible, though, for hackers to cross-reference this data and make their attacks far more potent.
The New Age of Consumer Data Protection
The number of data breaches has only been increasing, making consumer data security a serious concern.
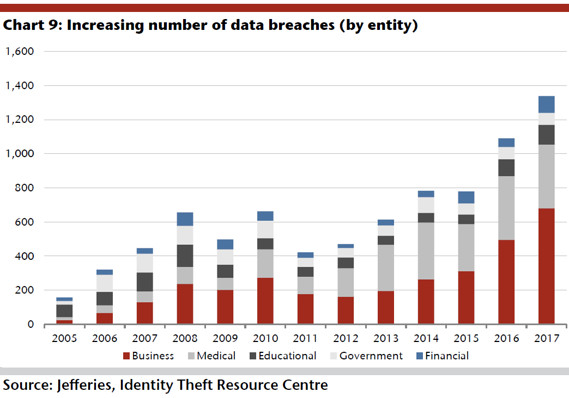
MarketWatch shares this chart on data breaches, as there have been a surge in hacking attacks targeting sensitive information. In the past few years, we have seen significant hacks from companies like Equifax, Target , Yahoo, Dropbox, the Democratic National Committee and many more.
Many of these breaches are related to the poor management of the company which holds your private and personal information. Many companies ask for your personal and private information in order for you to use their platform. What are they doing with this information? Companies have long profited from the collection of private information. Individuals should have the right to know how this information is used.
This year GDPR, passed in Europe, addresses consumer data privacy issues. The General Data Protection Regulation (GDPR) (EU) 2016/679 is a regulation in EU law on data protection and privacy for all individuals within the European Union and the European Economic Area. The GDPR aims primarily to give control to citizens and residents over their personal data and to simplify the regulatory environment for international business by unifying the regulation within the EU.
It’s more important than ever for people to fully understand how their data is being used.
We are building Bloom to bring identity and credit to the modern age.
Bloom Gives Users the Power to Take Back Their Data
At Bloom, we give users the power to take back their data. We give users the power to own their own data, and decide how it’s used, how it’s sold.
Bloom is a standardized, programmable ecosystem to facilitate on-demand, secure, and global access to credit services. Bloom is an end-to-end protocol for identity verification, risk assessment and credit scoring, entirely on the blockchain. Bloom offers solutions to cross-border credit scoring and identity fraud while at the same time expanding credit globally to new individuals and improving scoring methodology for all.
With Bloom:
- You own your data
- You control access to your data
- You decide when you share your data and who you share it with
We believe in a world where you finally control your own information and innovation can remove the inefficiencies of legacy systems.
Take back your data today.
Learn More About Bloom
- Check out the Bloom Website
- Come Chat on Bloom Telegram
- Read the Bloom Blog
- Read the Bloom Whitepaper
- What is Bloom?